Most systems rely on only one thing to gain access: username and password. While they constitute two pieces of information, in the world of cyber security, they’re just one “factor”: something you know. Alone or together, than can be easily transferred to a third party, digitally or via a yellow post-in note.
Real security relies on 2-factor, or even 3-factor authentication. The three factors are:
- something you know
- something you have
- something you are
The third factor is the realm of biometrics, now becoming much more widespread with the advent of smartphones containing a fingerprint reader. But there are many other forms of biometrics: retina scan, hand geometry, facial recognition, speech recognition, and others. However, as a general rule, biometric verification requires relatively sophisticated (and expensive) readers.
Adding the “something you have” as a second factor immediately provides an exponential leap in the level of security built into a system. There are a number of technologies which enable this second factor of authentication. Becoming more and more common, for example, is an SMS message to a pre-registered cellphone with a one-time password. Another common system is to implement a unique number generator, often called an “RSA Token”, which displays a number which changes every minute or so.
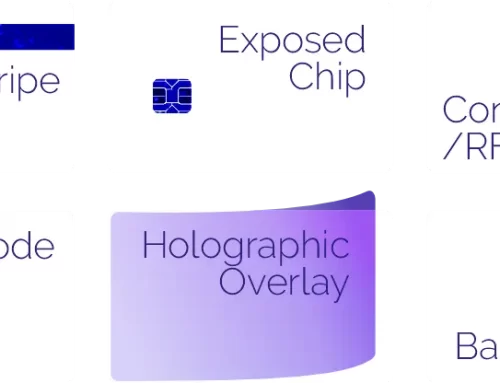
But a very easy, low-cost way to implement two-factor authentication is with the use of a smartcard. The smart ID card contains encoded data which only works in combination with a specific username and password. Only when both are present and correct can access proceed. This sort of technology curtails drastically the ability for hackers to gain access remotely to your network resources.
Most facilities do not really need 3-factor authentication, as that is what is typically used for military installations, nuclear power plants, and the like. But implementation of two-factor authentication can be surprisingly simple, and extremely cost-effective.